OnBoard™ IoT Security (OBIS) is built to that bar — key storage, CA operation, factory provisioning, end to end. Host both CA layers on OBIS, or keep your OEM CA on your existing PKI.
The Google Cast program carries security requirements across three operational areas. OBIS operates to those requirements end-to-end.
Google operates the Cast root, and each device carries a unique device certificate at the bottom. Between them sit two intermediate layers — OEM CA and Model CA. The Model CA and device certificate issuance always run on OBIS; the OEM CA is the variable.

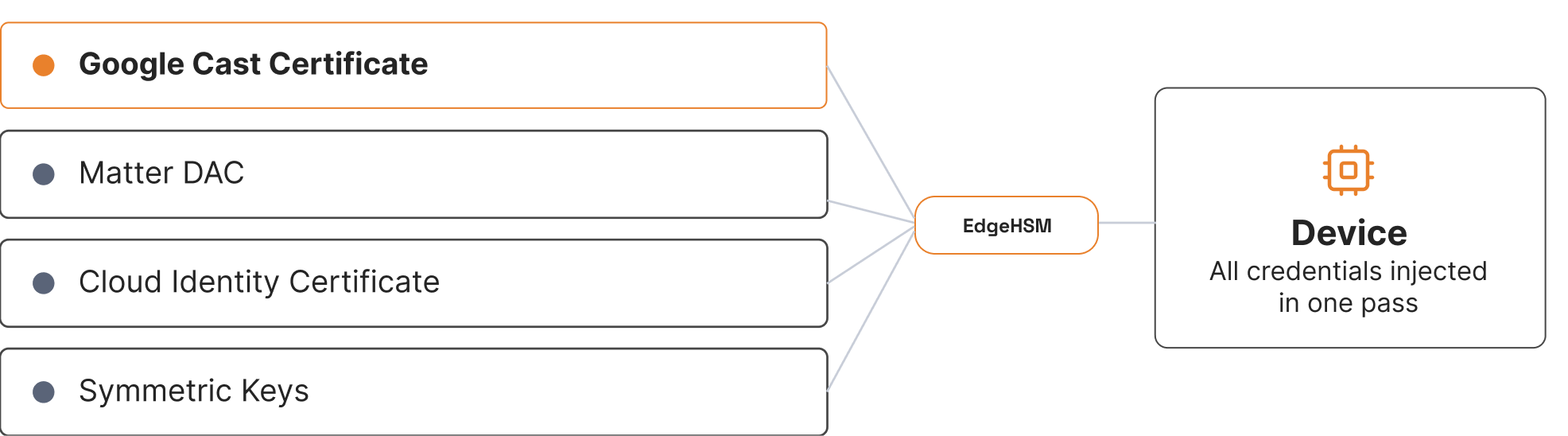
Devices with Chromecast built-in typically require multiple credentials — Cast, OEM cloud identity, Matter DAC, and OTA/local encryption keys — each provisioned through separate services and workflows. OBIS consolidates them into a single Production Version, provisioned in one production-line step.
Cast certificates expire and firmware requires ongoing updates, while CRA mandates security support throughout a device’s typical 5–10 year lifecycle. OBIS centralizes certificates, keys, SBOMs, and audit trails in one platform across the full device lifespan.
A 30-minute walkthrough covers your hosting model, your factory setup, and how OBIS maps to the program's security requirements — with your security architect,
not a sales deck.