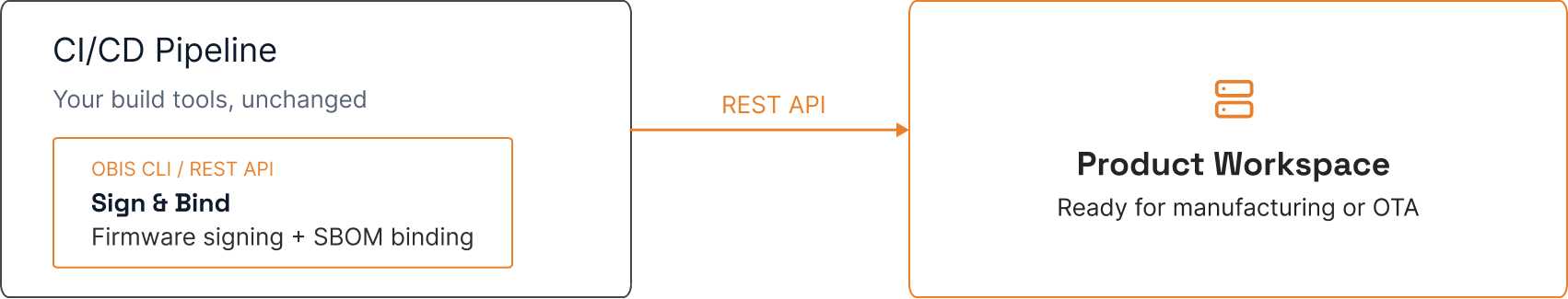
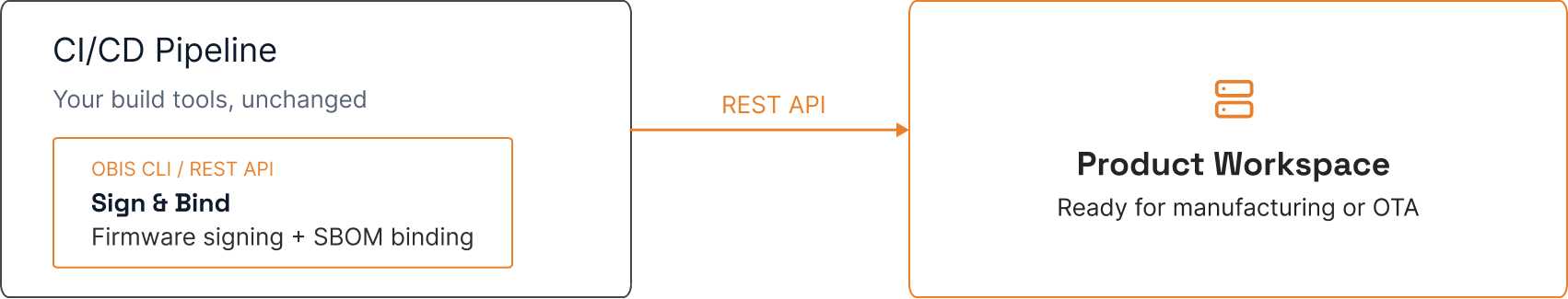
OBIS provides a CLI and REST API for firmware signing and SBOM binding. The signed firmware and its bound SBOM enter the Product Workspace and are ready for factory provisioning or secure OTA.
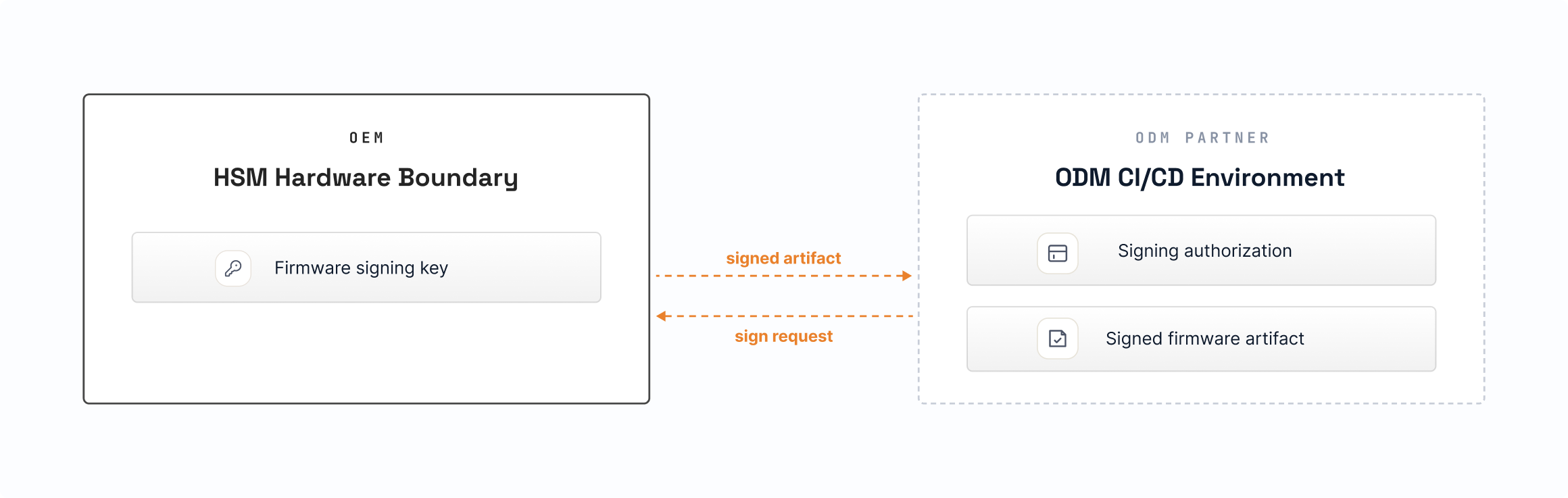
The ODM scenario is higher-stakes. OEMs need ODM partners to sign firmware in their own CI/CD environments. OBIS delegates signing capability: the ODM receives a scoped, revocable authorization — not the key itself. Multiple parties produce the OEM's signature — without ever holding the key.
A 30-minute demo walks through your build pipeline and shows how OBIS signing integrates without changing your tool chain.