The PKI module of OnBoard™ Secure Infrastructure (OBSI) issues and manages certificates for IoT devices. Every certificate is bound to a product, version, and device. Fresh, your root, or an industry root — OBSI runs the issuance layer beneath. When partners need to issue, they do so under scoped authorization, never by holding your CA private keys.
Every certificate is bound to a product, a version, and a device from the moment it is issued — and stays visible in that frame for its full lifecycle.
Certificate Profiles let you declare any X.509 specification — extensions, key usage, EKUs, validity policy, signing constraints — once. The engine handles every subsequent issuance, whether you author the profile or pick from the pre-built set.
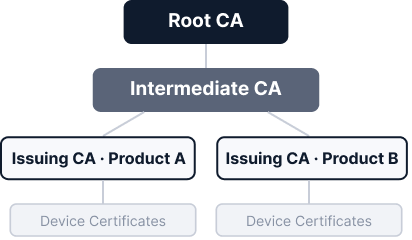
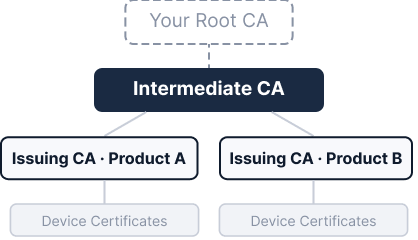
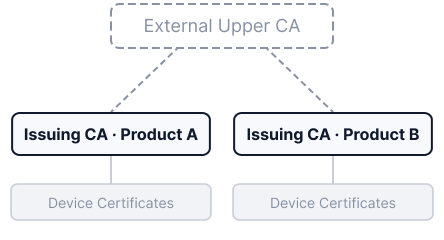
Factory layouts, partner relationships, and regulatory boundaries define your supply chain's structure. OBSI PKI builds CA hierarchies that follow that structure — at whichever depth you hand the hierarchy over to us.
Multi-party device programs need partners, factories, and branches to issue certificates locally. OBSI PKI separates the right to issue from the keys that sign — so collaboration scales without your CA private keys ever leaving their hardware boundary. Authorization scope and audit are bounded by the PKI Workspace — the same boundary unit shared with KMS and SEMS.
A 30-minute demo covers your CA topology, the Profile System, and how partners issue under scoped authorization without ever holding your CA private keys.